To MicroTik or to MikroTik? I can never remember.
A collection of notes on MikroTik configuration & Maintenance.
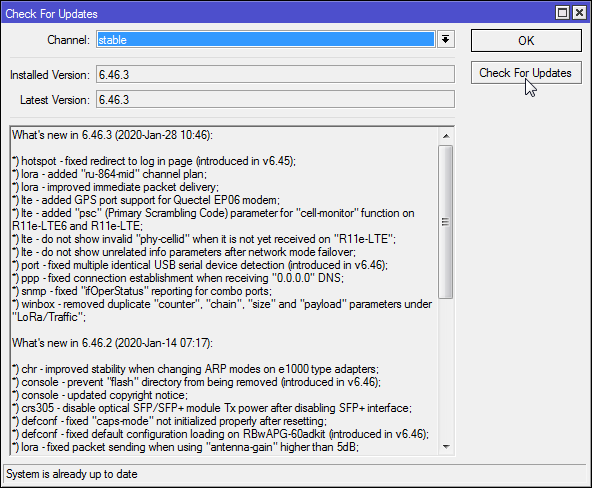
Upgrade your firmware!
One of my clients had their MikroTik compromised in 2018. MikroTik had published an updated firmware version a few months before that mitigated the "attach vector", but unfortunately the device hadn't been updated in time. The end result? VOIP accounts compromised, about $300 of voice calls charged.
So the lesson learned is: always keep your MikroTik firmware up to date! How? You have two options (using WinFig):
(1) Check for Updates button on the QuickSet page
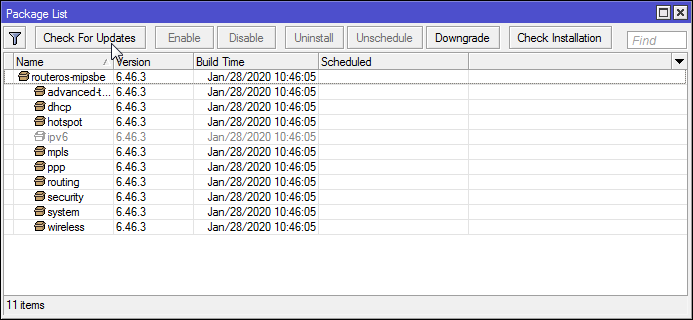
(2) or System → Packages, "Check for Updates"
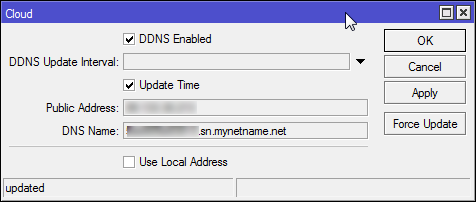
MikroTik Dynamic DNS Service
IP → Cloud, and ✓ to enable!
Set up L2TP VPN Server
Before you start, update your firmware.
(1) Add firewall rules:
/ip firewall filter
add action=accept chain=input comment="Allow L2PT VPN access" \
dst-port=500,1701,4500 protocol=udp
add action=accept chain=input protocol=ipsec-esp
add action=accept chain=input protocol=ipsec-ahMove these rules to the top of your input chain.
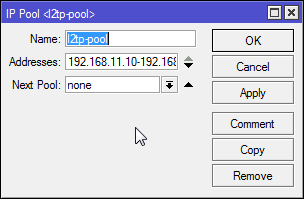
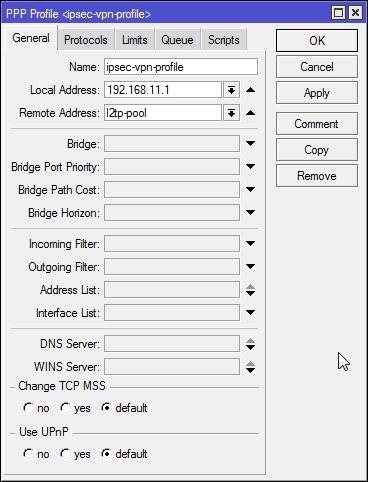
(2) Set up an L2TP profile (this is a way of setting defaults for several logins, or "secrets"):
Create a pool of addresses for your clients:
IP→Pool→+
PPP→Profiles→+
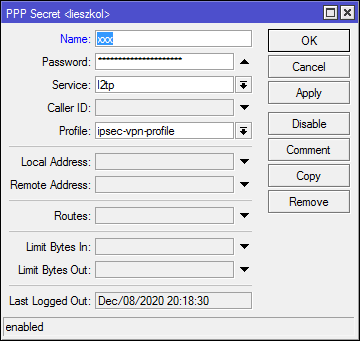
(3) Add logins, or "secrets":
PPP→Secrets→+
(4) Enable L2TP:
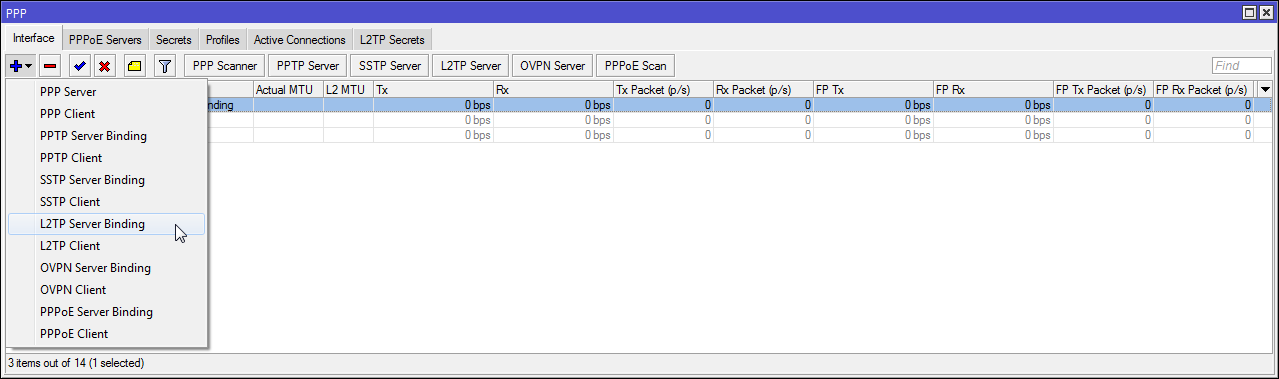
PPP→Interface→L2TP Server
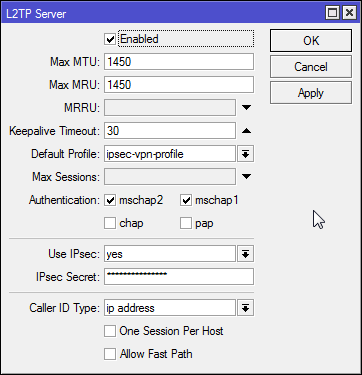
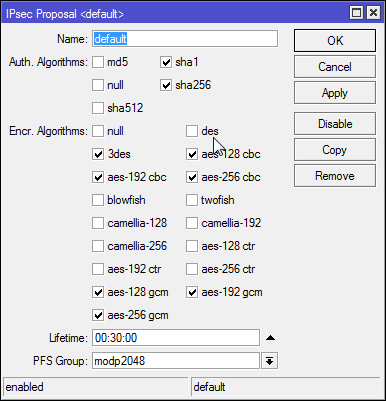
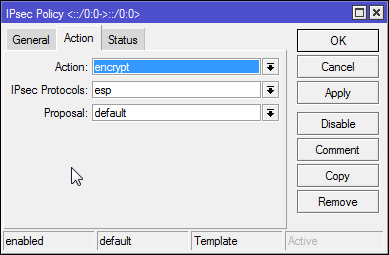
Current RouterOS versions will automatically configure IPSec for you at this point. They will look something like this, you can mess with it but it's easy to mess it up:
IPSec→Proposals
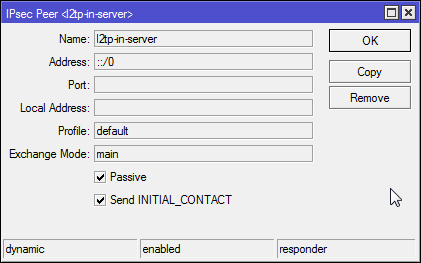
IPSec→Peers
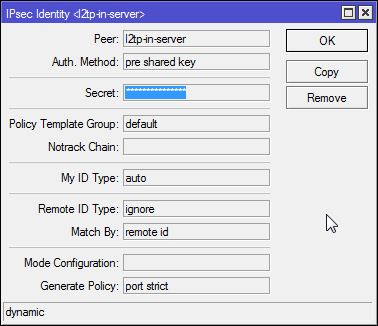
IPSec→Identities
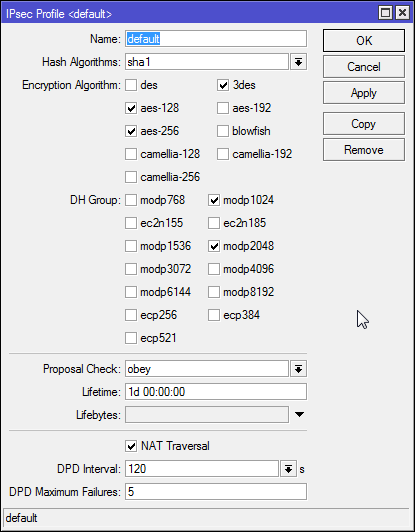
IPSec→Profiles
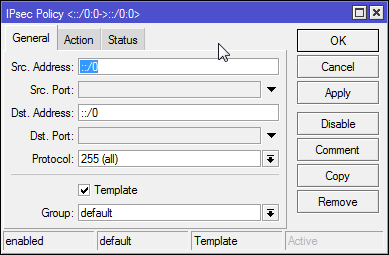
IPSec→Policies
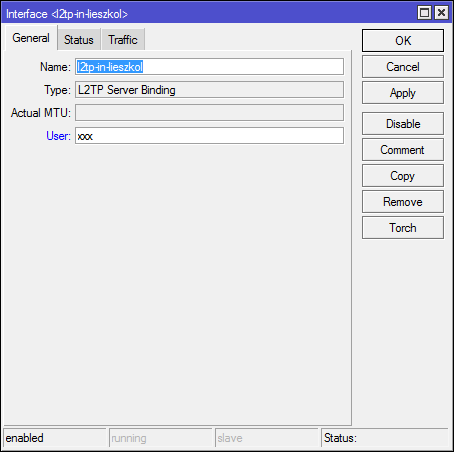
(5) Optionally create an L2TP server binding:
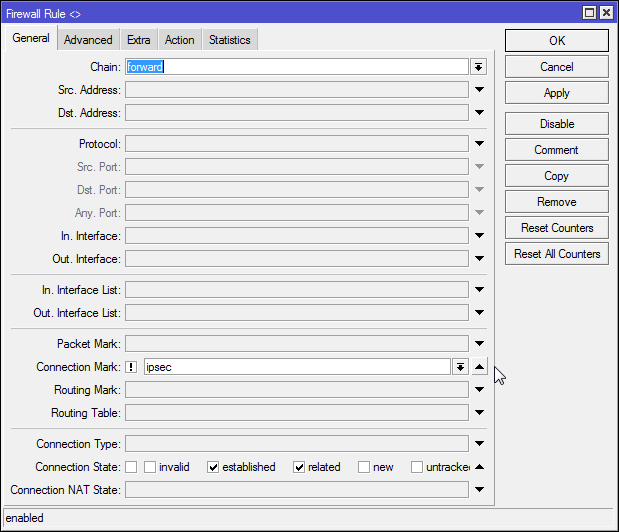
(6) Adjust fasttrack
Fasttrack can mess with your L2TP, slowing down connections. To get around this, do:
/ip firewall mangle add action=mark-connection chain=forward comment="mark ipsec connections to exclude them from fasttrack" ipsec-policy=out,ipsec new-connection-mark=ipsec
/ip firewall mangle add action=mark-connection chain=forward comment="mark ipsec connections to exclude them from fasttrack" ipsec-policy=in,ipsec new-connection-mark=ipsecThen, in your firewall, find your default fasttrack rule and set connection-mark=!ipsec:
Sources/reference:

